Endpoint security or endpoint protection is an approach to the protection of computer networks that are remotely bridged to client devices. The connection of endpoint devices such as laptops, tablets, mobile phones, Internet-of-things devices, and other wireless devices to corporate networks creates attack paths for security threats.[1][2] Endpoint security attempts to ensure that such devices follow a definite level of compliance to standards.[3]
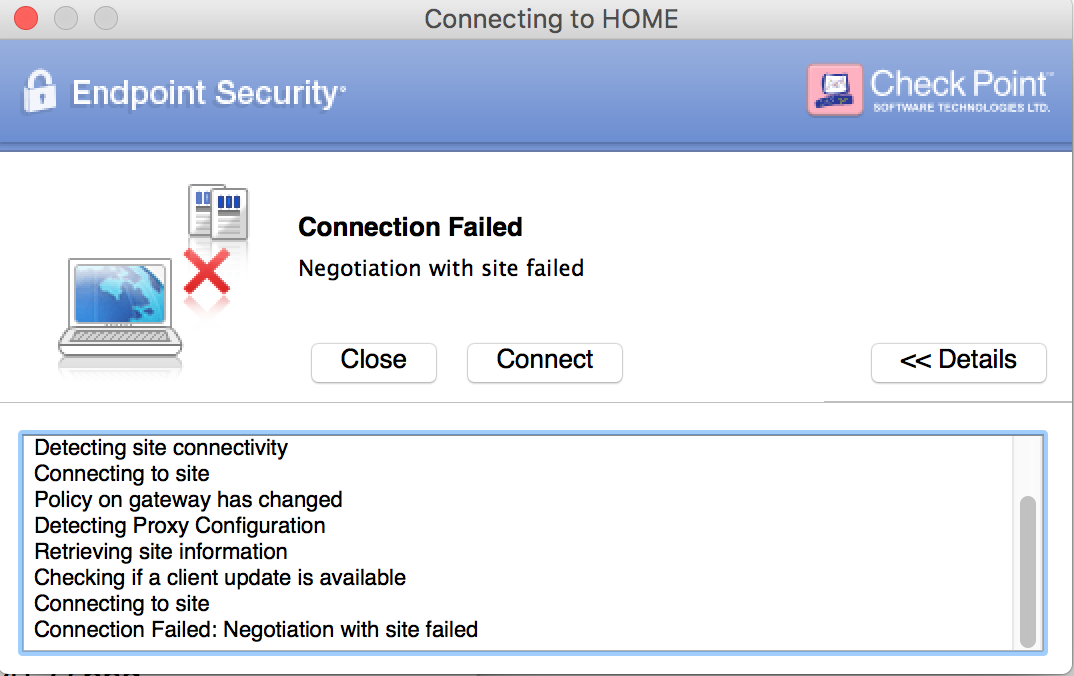
Tried the private build and the published build for 10.11.1 and 10.11.2 Nothing works. This IS a Fortinet problem other VPN Clients like Tunnelblick work without any problems. To excuse the non existing effort on their side by waiting for Apple to solve THEIR client problems is ridiculous. Kaspersky Endpoint Security 10 for Mac protects computers running under Mac OS X against malicious software. Following is information about the status of known university-wide issues with OS X 10.11 (El Capitan) at Indiana University. Pulse Secure may not be able to establish a VPN connection and may report Keychain errors. Install Pulse Secure 5.1.5 or later, available from IUware. Office 2016 applications may experience frequent hangs and crashes.
The endpoint security space has evolved over the last several years away from limited antivirus software and into a more advanced, comprehensive defense. This includes next-generation antivirus, threat detection, investigation, and response, device management, data leakprotection (DLP), and other considerations to face evolving threats.

Corporate network security[edit]
Endpoint security management is a software approach that helps to identify and manage the users' computer and data access over a corporate network.[4] This allows the network administrator to restrict the use of sensitive data as well as certain website access to specific users, to maintain, and comply with the organization's policies and standards. The components involved in aligning the endpoint security management systems include a virtual private network (VPN) client, an operating system and an updated endpoint agent.[5] Computer devices that are not in compliance with the organization's policy are provisioned with limited access to a virtual LAN.[6]Encrypting data on endpoints, and removable storage devices helps to protect against data leaks.[7]
Client and server model[edit]
Endpoint security systems operate on a client-server model, with the security program controlled by a centrally managed host server pinned[clarification needed] with a client program that is installed on all the network drives.[8][9] There is another model called software as a service (SaaS), where the security programs and the host server are maintained remotely by the merchant. In the payment card industry, the contribution from both the delivery models is that the server program verifies and authenticates the user login credentials and performs a device scan to check if it complies with designated corporate security standards prior to permitting network access.[10][11]
In addition to protecting an organization's endpoints from potential threats, endpoint security allows IT admins to monitor operation functions and data backup strategies.[12]
Endpoint Security Vpn 10.11 Download
Endpoint protection platforms[edit]
Endpoint Security Vpn 10.11 Crack
Endpoint protection platforms (EPP) are solutions that can be deployed on the endpoint to protect against file-based, fileless, and other types of malware, through prevention and investigation, and remediation capabilities.[13] Several vendors produce systems converging EPP systems with endpoint detection and response (EDR) platforms – systems focused on threat detection, response, and unified monitoring.[14]
See also[edit]
References[edit]
- ^'Endpoint security management overview'. Retrieved July 22, 2015.
- ^'What is endpoint security and how does it work?'. Retrieved August 21, 2015.
- ^'What is endpoint security?'. Retrieved July 22, 2015.
- ^'Endpoint security & network protection'. Retrieved October 7, 2015.
- ^'Endpoint security standard'. October 7, 2015.
- ^Endpoint security and compliance management design guide. Redbooks. October 7, 2015.
- ^'What is Endpoint Security?'. Forcepoint. August 9, 2018. Retrieved August 14, 2019.
- ^'Centrally managed host server'. Microsoft. October 7, 2015.
- ^'Client-server security'. Exforsys.
- ^'mobile devices especially vulnerable'.
- ^'PCI and Data Security Standard'(pdf). October 7, 2015.
- ^'12 essential features of advanced endpoint security tools'. SearchSecurity. Retrieved August 14, 2019.
- ^Inc, Gartner. 'Endpoint Security and Protection Software Reviews'. Gartner. Retrieved December 24, 2019.
- ^Gartner (August 20, 2019). 'Magic Quadrant for Endpoint Protection Platforms'. Retrieved November 22, 2019.
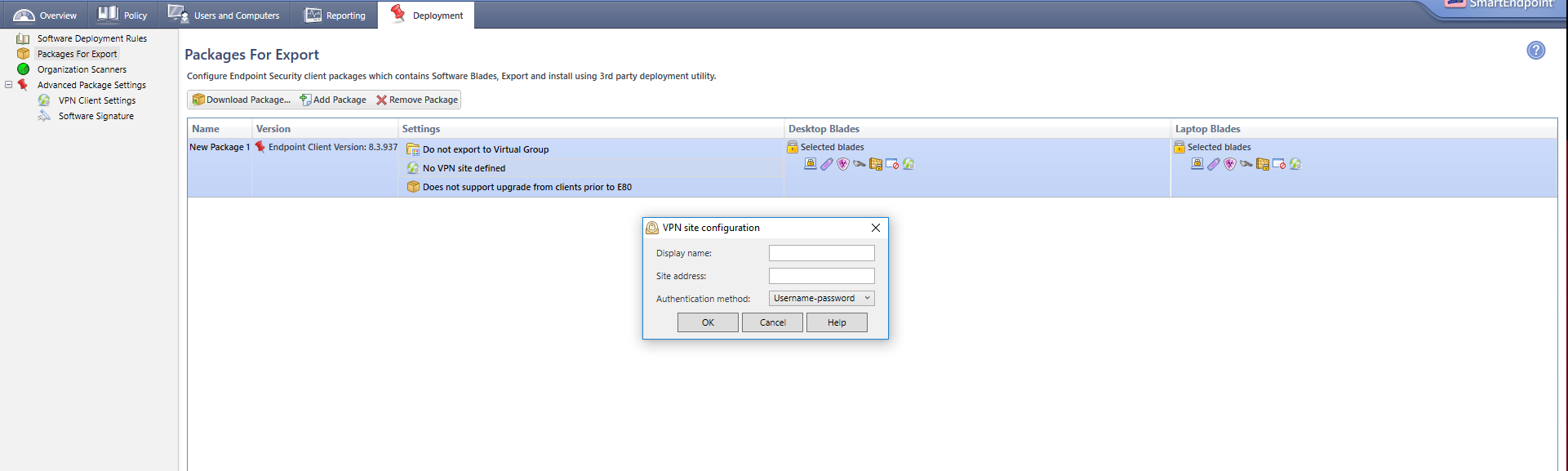
HI,
I've read the 'How to' for Endpoint Security packages, and it does pretty much achieve what I want, however, the VPN Tunneling section 'Encrypt all traffic and route to gateway' option (which is now checked), this needs to be a user configurable option. In its current state, the box is checked and greyed out. I need it un-greyed out (?) (along with the 'Enable Always-Connect option)
The Admin guide also says you can change this, but when i run Admin.bat, its greyed out too.
Is this something I need to do via Dashboard or changes in the trac.config file?
Thanks
KB